Deploying the GreenRADIUS FIDO2 App
Prerequisities
- A PC running 64-bit Windows or macOS
- YubiKey or other FIDO2 token
- GreenRADIUS v5.1.2.2 or later
- A valid GreenRADIUS license with the "FIDO2 for RADIUS, LDAP, and 2FA API Integrations" module enabled
- Our GRS FIDO2 Authenticator App v2.1.2 or later
Instructions
1. GreenRADIUS Configuration
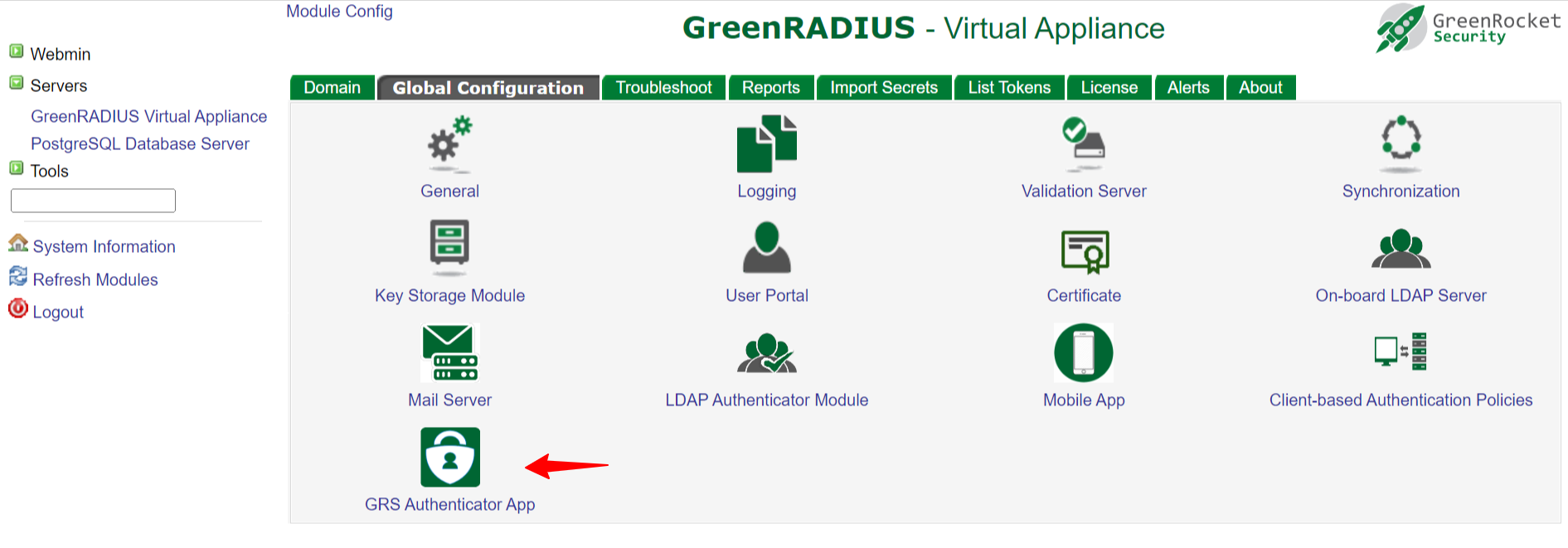
- Go to Global Configuration → GRS Authenticator App.
- Configure the following fields:
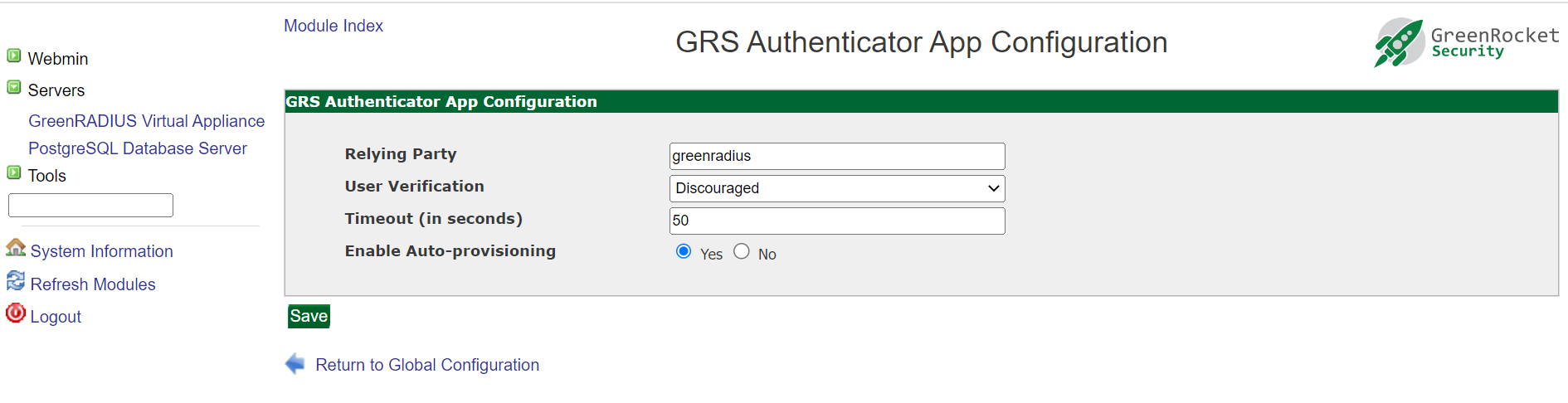
- Relying Party: this should be the same as the GreenRADIUS hostname.
- The relying party name should resolve to the IP of GreenRADIUS. This can be done by adding a DNS entry to the host file of the local system.
- Changing the Relying Party will invalidate all the previously registered tokens.
- User Verification:
- Discouraged: Users are not prompted for FIDO2 token PINs during login attempts
- Preferred: Users are prompted for PINs during login attempts
- Required: Users are always prompted for PINs during login attempts
- Timeout (in seconds): defaults to 60.
- Enable Auto Provisioning: defaults to Yes.
2. Application Installation
2a. Installation on Windows
- Run the GRS FIDO2 Authenticator app installer
- Once the installation is complete, run the application
2b. Installation on macOS
Click on the macOS installer and drag the Green Rocket Security Authenticator icon into the Applications folder, then launch the application.
3. Application Configuration
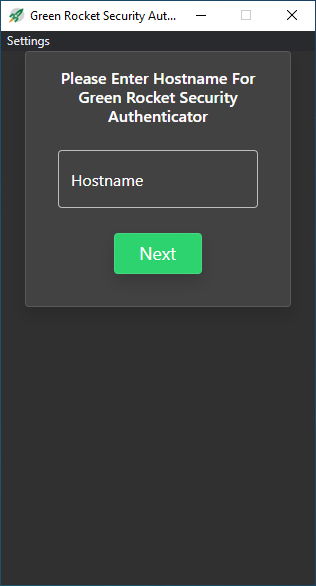
Once you have launched the GRS FIDO2 Authenticator app, you will need to enter the hostname of GreenRADIUS:
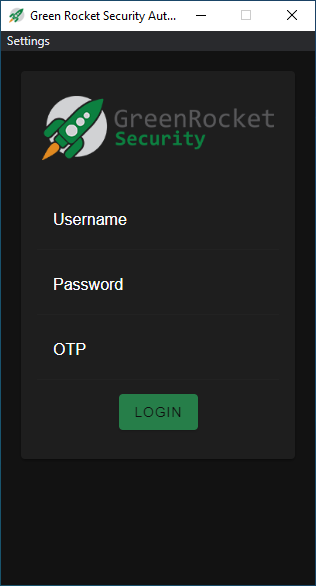
Next, enter your username, password, and an OTP from a token assigned to the user. (A Temporary Token will also work.)
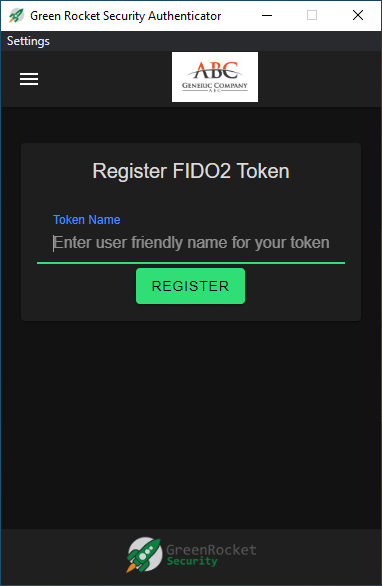
If a FIDO2 token is not already registered to you, you will automatically be redirected to the FIDO2 token setup screen upon successful login. Here, you will enter a human-readable name for your token (such as the YubiKey's serial number).
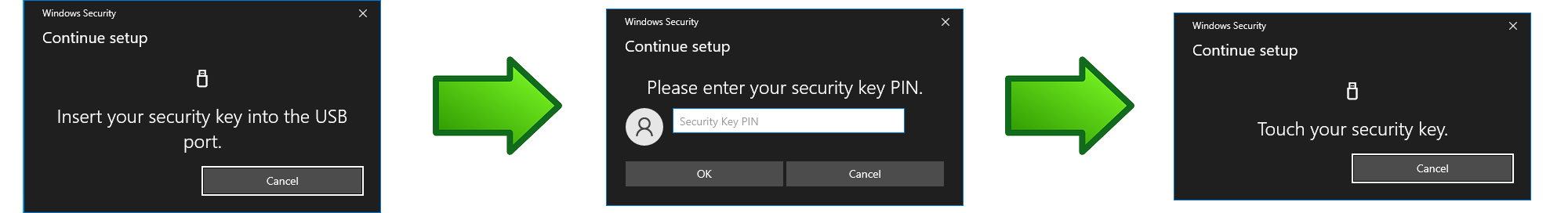
The standard Windows FIDO2 dialog will now appear. At this point you will need to insert your FIDO2 token into the computer's USB port if you have not already. Enter your FIDO2 token's security PIN (if applicable), and then touch the FIDO2 token when prompted.
The FIDO2 token will now be registered to the user in GreenRADIUS.
To test, send an authentication request using the RADIUS Test feature of GreenRADIUS on the Troubleshoot tab or from another configured RADIUS client
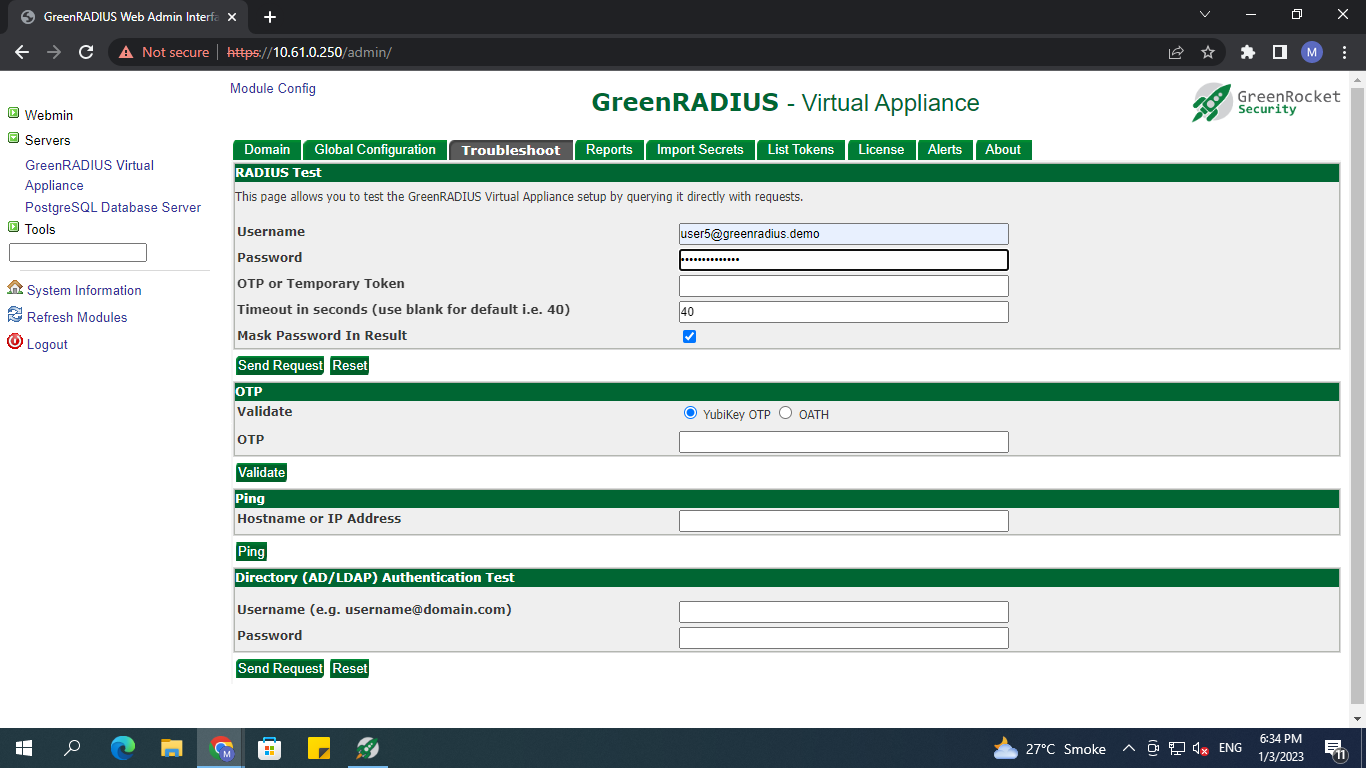
Upon sending the request, you should see a notification from the app:
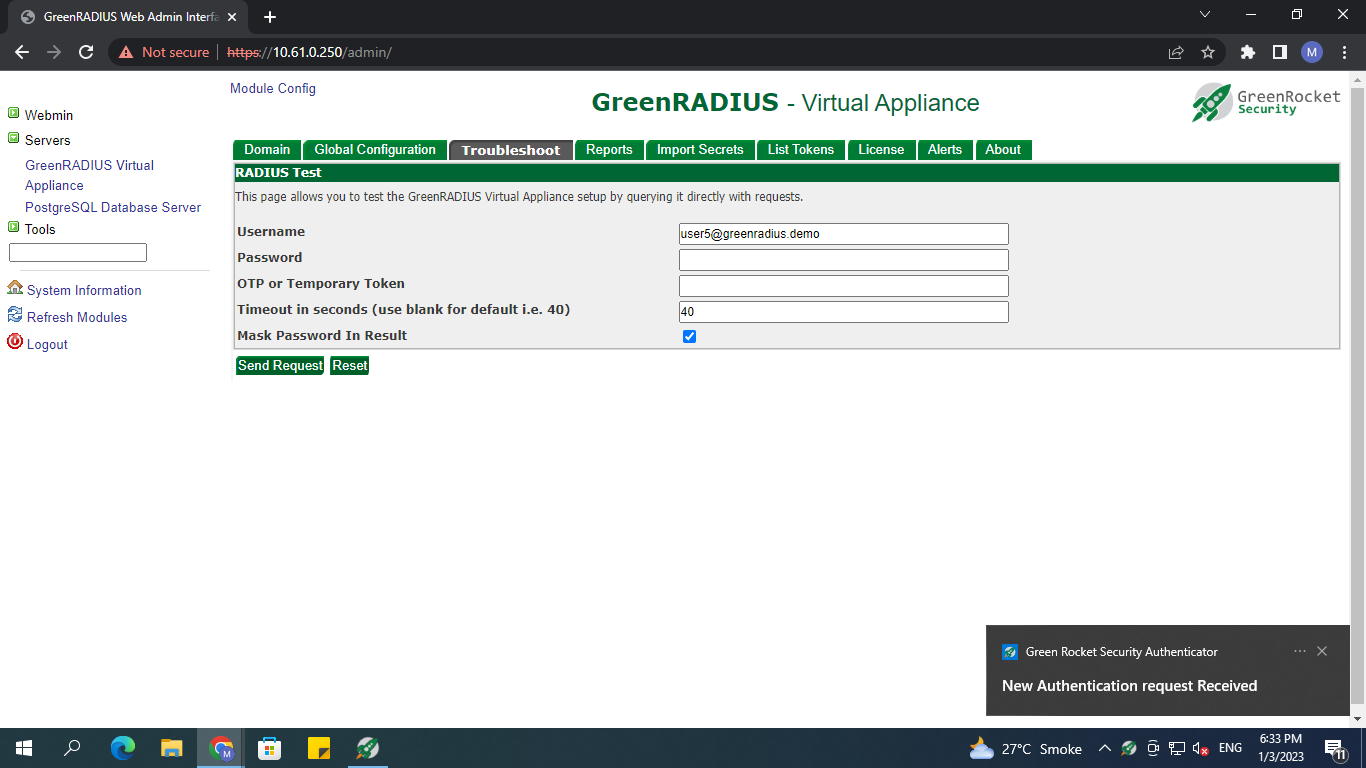
The request will appear in the app dashboard. You can now click the request to decide whether to approve or reject it.
If you decide to approve the request, the standard Windows FIDO2 dialog will appear. Enter the PIN (if prompted), and touch the FIDO2 token. The login should then be successful if performed within the timeout period.
For browser-based logins on any operating system
If users are on a Linux, Android, iOS, or some other platform, or if on Windows or Mac and our FIDO Authenticator App is not installed nor desired, users can complete their FIDO2 login attempt on a browser. The user will need to visit https://[hostname_of_GreenRADIUS]/client. Then, the user will need to log in, and register a FIDO2 token if one is not already registered. Then, when the user logs into any RADIUS or LDAP client, the user will be prompted to complete his or her login attempt following the FIDO2 prompts.
© 2026 Green Rocket Security Inc. All rights reserved.